Mitigating Living off the Land Attacks, C2 Abuse with Insider Risk Monitoring
The DTEX i³ Team has issued a new Insider Threat Advisory following growing concern over the potential for malicious insider threats to weaponize trusted workspace applications to exfiltrate data and evade detection.
Lenient Access Control Policies for Personal Webmail Increases Data Loss Risk
This Threat Advisory provides information on the risks associated with the use of ChatGPT and other AI chat tools, and steps for early detection and mitigation.
Insecure Web Apps Creating High Risk for Insider Abuse
This Threat Advisory lists common web application categories prone to exploitation by malicious insiders.
MOVEit - CVE-2023-34362
DTEX advises customers to run the provided queries in this Threat Advisory within the DTEX InTERCEPT platform.
People's Republic of China - Volt Typhoon
iTA-23-03 highlights Volt Typhoon and the detection capability within DTEX InTERCEPT to uncover behaviors of users.
TOP INSIDER RISK RESOURCES
AS RECOMMENDED BY DTEX i³
-
2024 Insider Risk Investigations Report - Foreign Interference: Special Edition
DTEX i³
-
Guiding Principles for Insider Threat
MITRE Corporation
-
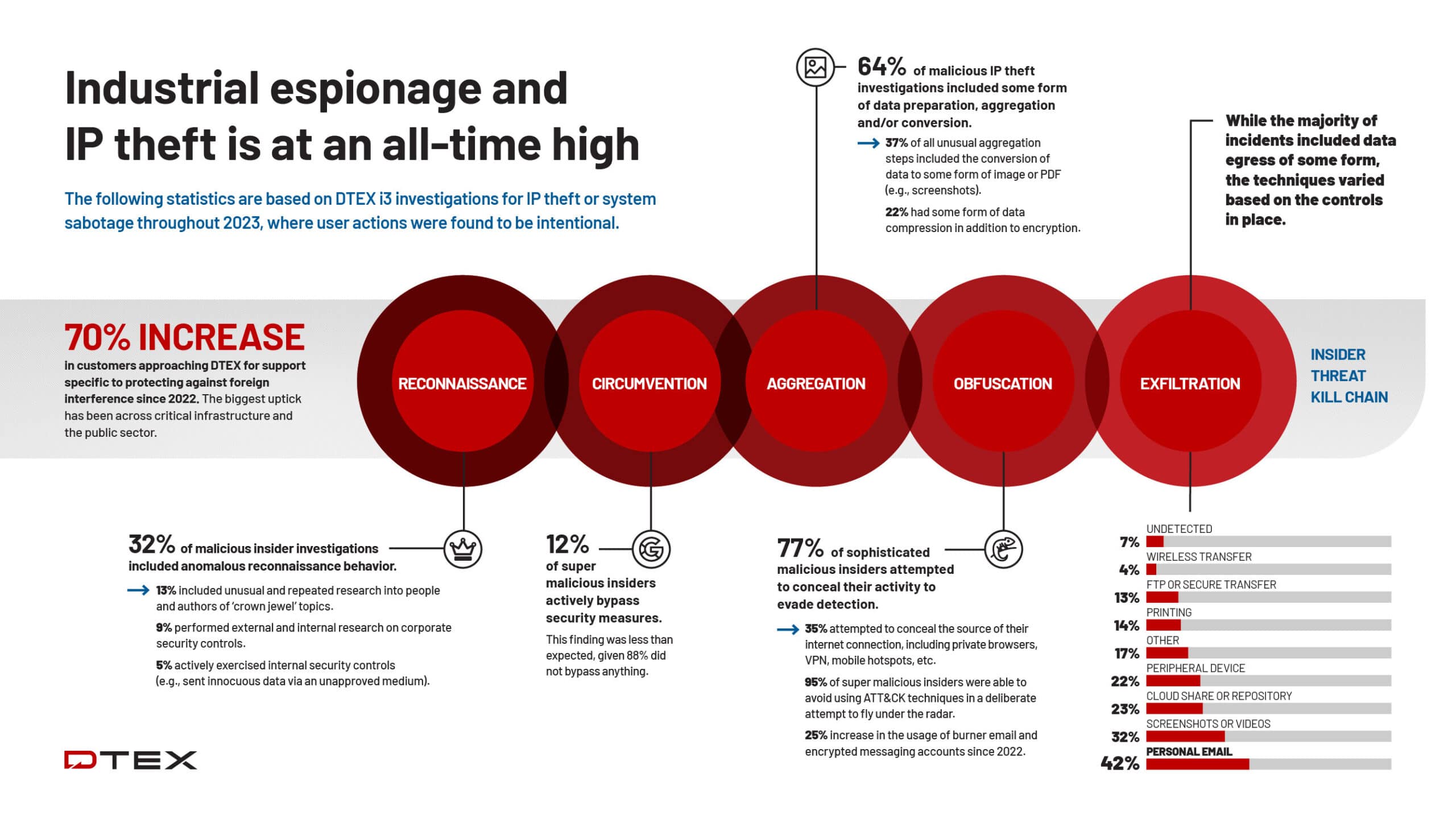
Insider Threat Kill Chain: Behavioral Insights of Malicious and Super Malicious Insiders
DTEX i³
-
Insider Threat Toolkit
Center for Development of Security Excellence, Defense Counterintelligence and Security Agency
-
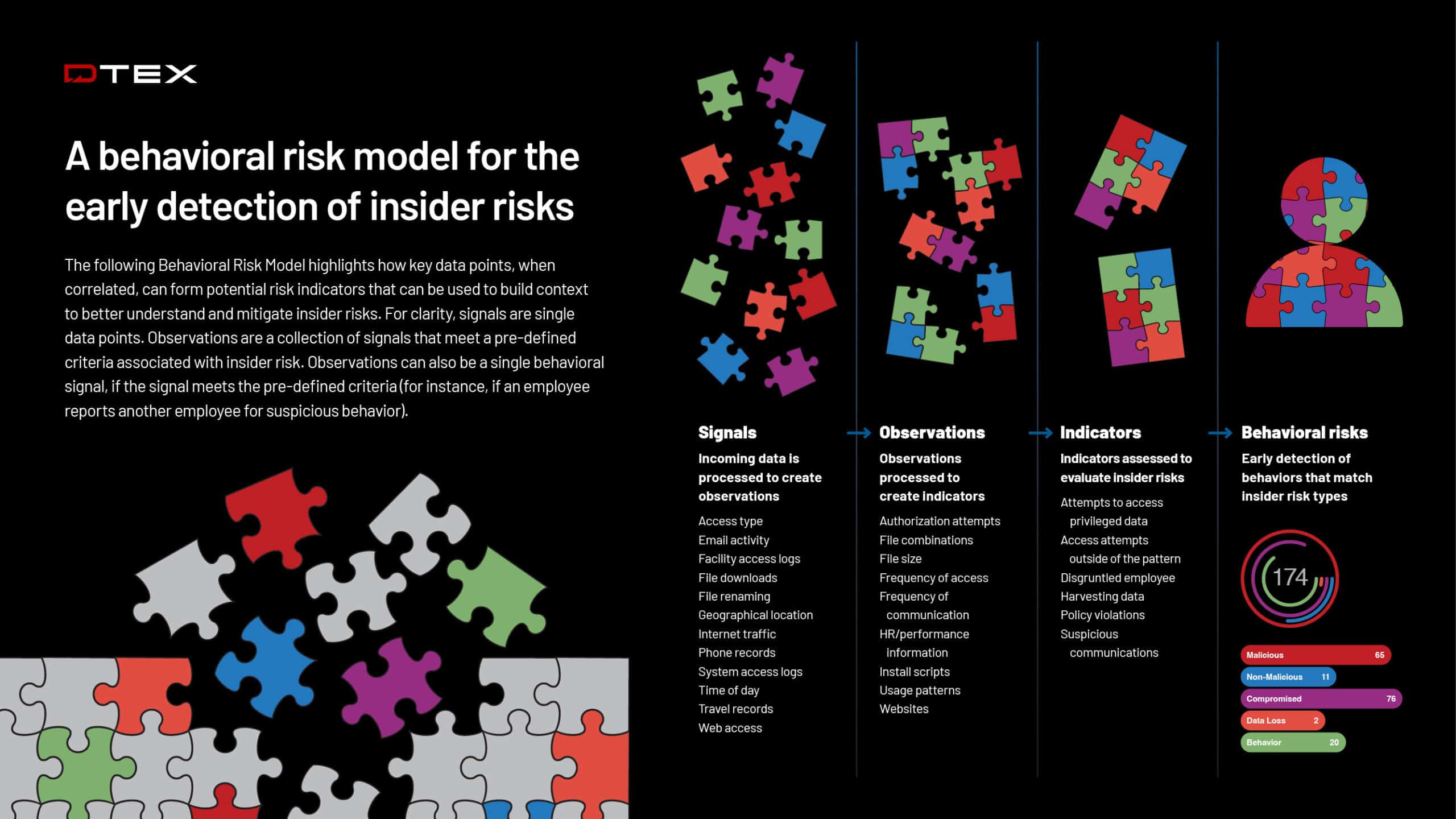
Behavioral Risk Model for Early Insider Risk Detection and Mitigation
DTEX i³
-
Insider Threat Program Maturity Framework
National Insider Threat Taskforce
-
2023 Cost of Insider Risks Global Report
Ponemon Institute and DTEX Systems
-
Common Sense Guide to Mitigating Insider Threats
Software Engineering Institute, Carnegie Mellon University
-
Insider Risk Mitigation Framework
National Protective Security Authority
-
Legal Considerations for Employee IT Monitoring
National Protective Security Authority
-
Insider Risk Mitigation Program Evaluation (IRMPE)
Cybersecurity and Infrastructure Security Agency
-
HR’s Role in Preventing Insider Threats
Cybersecurity and Infrastructure Security Agency
-
Insider Threat: The Theft of Intellectual Property in Windows 10
SANS Institute
-
Seven (Science-Based) Commandments for Understanding and Countering Insider Threats
Eric L. Lang
Actionable Insights and Assets
Popular Insider Risk Insights
About DTEX i³
Powering Next Generation
Insider Risk Management
DTEX i3 enables enterprise and federal entities to uplift their insider risk capability maturity to detect and prevent the most sophisticated insider risks from materializing into data loss events. The team offers a comprehensive set of insider risk services, including investigation support, insider risk assessments, emerging risk insights, reporting, and more. Download the i3 Solution Brief to view the full set of services.
To talk to a member of the i3 team about the latest research or early warning indicators, request a Threat Briefing.
Request a Threat Briefingi³ Mission
DTEX i³ Mission Statement
DTEX i³’s mission is to uplift enterprise security by proactively detecting and mitigating insider risks.
Combining 20 years of insider risk experience with our potential risk indicators, we empower organizations to stay resilient, and maintain control of their public narrative and global success.
Importantly, DTEX i³ often discovers wider security threats that extend beyond insider risks. Such external threats are typically the outcome of an insider incident, not the intention of the insider.
In both cases, DTEX i³ prioritizes detection and deterrence, helping organizations to do away with reactive incident response.
Contact i³