Integrations are critical for efficient and effective insider risk management. This might sound like a simple statement, but there is a lot that goes into it. No cybersecurity tool today can operate effectively in isolation. There are two critical considerations when looking at integrations. First is the quality and format of the data. Second is the direction of the integration, and the best place for the data to reside.
Data quality is extremely important. Poor quality data only results in high rates of false positives. The wrong format can result in critical data sets being missed. SYSMON is a very popular data set that includes a ton of information, but most is irrelevant – at least from a cybersecurity perspective. At DTEX, we do our own data collection that is curated specifically for cybersecurity. We only collect what is necessary (3-5MB per endpoint daily) and it is tamper proof. For our integration with Splunk, this is extremely important.
DTEX and Splunk: A Powerful Push Integration
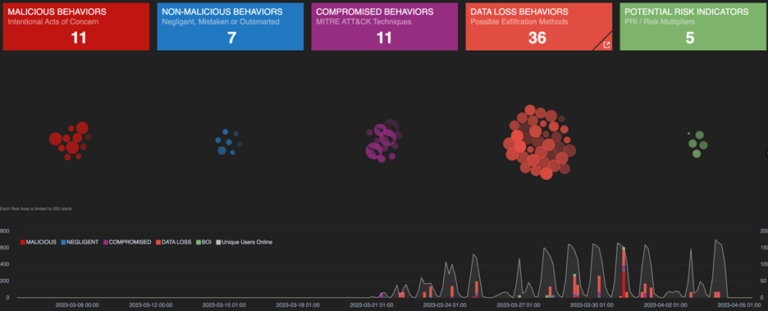
Many of our partners that support Splunk leverage the DTEX Splunk Forwarder and the DTEX Splunk App. Both can be found via the Splunk App Store. This is an example of a push integration. DTEX can forward our raw log data, enriched log data, or just enriched alerts into Splunk based on the customer’s preference. Where DTEX provides significant value to the Splunk customer is by providing more than 300 behavior-based detections out of the box. Many Splunk customers struggle to find data scientists to develop their own custom detections in Splunk. With DTEX they get immediate value with the ability to customize any of our out-of-the-box behavioral-based detections, and by having better visibility within Splunk Enterprise Security thanks to the DTEX Splunk App.

DTEX and CrowdStrike: A Powerful Pull Integration
An example of a pull integration is the integration between DTEX and CrowdStrike. Where CrowdStrike is a leader in vulnerability management on the endpoint, DTEX is a leader in insider risk and threat detection and is essentially a flight recorder for every endpoint. When CrowdStrike generates an alert upon detecting malware, the API sends the alert to DTEX. In the DTEX console, the analyst can set the time range before and after the alert to better understand the origin of the risk, and exactly what happened if it loaded successfully. This represents significant time savings and the ability to provide an informed and proactive response to a risk before it turns into a threat.
These are just two examples of integrations that have been developed with our technology alliance partners. Our partners use them to significantly speed up the time to value for customers and reduce the costs to manage the integrations. Customers are requesting additional integrations every day and there are dozens more available. Follow any of the links below for more information:
DTEX InTERCEPT for CrowdStrike Falcon
DTEX InTERCEPT for Microsoft 365-E5
If you’re interested in becoming a partner, contact us to learn more.
Topics
Subscribe today to stay informed and get regular updates from DTEX Systems





