For the past 20 years I have worked for multiple security start-ups, primarily in the endpoint space. In my interviews with the press, one question has consistently come up: “Are you worried about competing with Microsoft?”
In most cases, the answer has been “no”. Typically, the companies I worked for were two steps ahead of Microsoft. Today, that is much less the case as Microsoft has done a great job of maturing its underlying products. As the endpoint security market matures against a slowing economy, 0.01% difference in detection capability is less relevant.
Accelerating Time to Value with DTEX and Microsoft
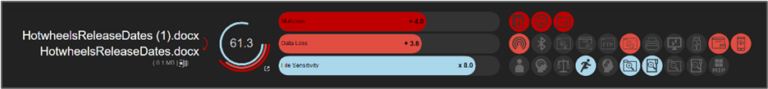
DTEX InTERCEPT complements Microsoft 365 E5 by correlating the unique alerts from all Microsoft products into a comprehensive risk score. Understanding human behaviors at the beginning of the Insider Threat Kill Chain is what makes this approach so effective at getting “Left of Boom” and intervening before a significant breach occurs.
DTEX and Microsoft Defender
The first complementary feature is how DTEX InTERCEPT complements Microsoft Defender. Like other EDR tools, Microsoft Defender does a good job at detecting malware and reporting on it. DTEX provides all the additional details that Microsoft Defender does not collect by acting as a flight recorder for every endpoint to provide detailed context of exactly what happened before, during and after the malware event.
DTEX and Microsoft Information Protection and Governance (Purview)
The File Lineage capability in DTEX InTERCEPT significantly complements the Microsoft Information Protection and Governance module (previously known as Microsoft Purview). As a traditional DLP technology, Purview provides solid file classification capabilities and protection against unintentional data loss incidents. From this perspective, DTEX can ingest the tagging from Purview to provide additional context to our risk score for every file in the Microsoft environment. In addition to the tagging, DTEX looks at who created the file, who has touched it, who has changed it, and if it was part of an unusual aggregation with other files. This additional context adds significant value, establishing user intent in relation to how they interact with the data, allowing for the early identification of risky behavior.
DTEX and Microsoft Defender for Cloud Apps
Whether it’s approved or not, DTEX profiles the endpoint access to all web-based resources to look for suspicious SaaS-based uploads and anomalous behavior in real-time (all without any configuration). User and peer group anomaly detection is always on with coverage for Windows, macOS, Linux, Citrix, VMware and cloud-based environments (e.g. AWS Workspaces).
DTEX and Microsoft integrate to make a very compelling case for partners positioning insider risk management. DTEX can also proactively send our alerts into Microsoft Sentinel for additional correlation of risk indicators.
The DTEX opportunity for partners is significant; not only can you drive value for your Microsoft 365 E5 clients, but you can generate additional sales volume and margin with InTERCEPT.
Contact us to discuss how you and your customers can maximize the DTEX-Microsoft opportunity.
Subscribe today to stay informed and get regular updates from DTEX Systems





