This is the third post in our blog series discussing Insider Threat Surveillance vs. Insider Risk Management tools. Read the previous posts here.
Scalability and Total Cost of Ownership are critical factors in almost every enterprise IT operation, including security. In today’s dynamic environment, organizations need solutions that reduce demands on scarce security and compliance staff, not complicate their lives and increase operating costs. They need solutions that can be rolled out quickly and economically without a need for an abundance of new infrastructure.
Likewise, commercial organizations need solutions that can grow with them, be deployed with minimal impact on the workforce, and not interrupt important and necessary workflows. One needs only look at traditional data loss prevention solutions with their myriad rules dictating which users can conduct which actions with each set of data—in advance—to understand the challenge of rolling out and maintaining a solution across large groups of users.
Scalability is especially important when addressing insider risk, data loss prevention and user behavior analytics. Unfortunately, Insider Threat Surveillance solutions cannot meet this need. The volume of data collected when capturing and processing video quickly adds up. Their requirements for system resources and network bandwidth are intensive by nature, requiring larger than normal processing power from the endpoint device and additional cloud storage.
Similarly, with such a diverse and distributed workforce, device types, and operating systems, ubiquitous support for MacOS, Windows, Linux, Citrix and Android are imperative to provide true enterprise coverage and visibility. Legacy insider threat surveillance tools are no longer able to provide that ubiquity based on operating system configuration upgrades and changes focusing on security and privacy. Look at Apple’s MacOS Monterey release for example.
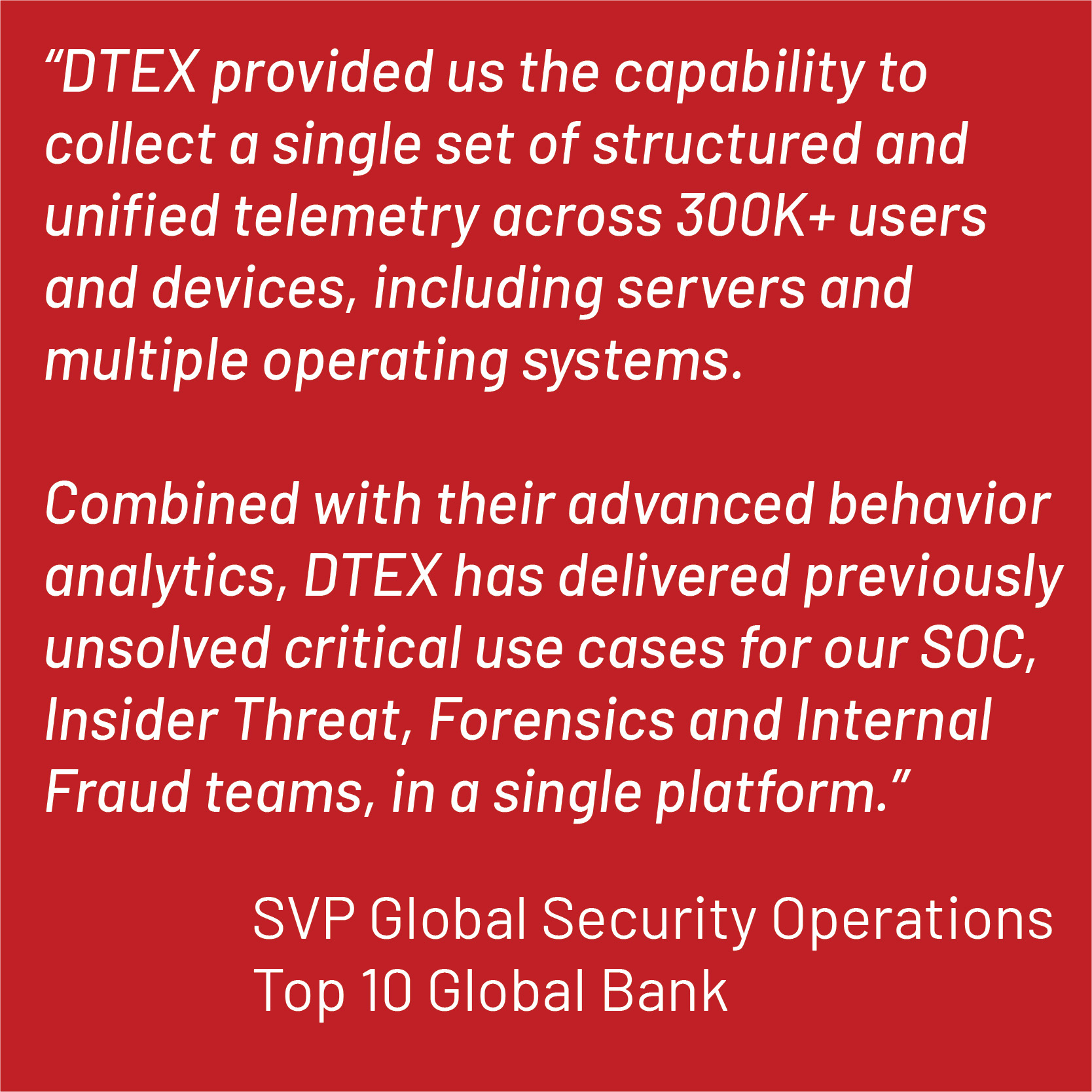
Protecting against insider threats requires solutions that can discern between legitimate use and malicious intent and be deployed quickly at tremendous scale. DTEX installs across hundreds of thousands of endpoints in only a few hours and begins protecting information immediately with analytics based on proven human behavioral patterns. DMAP+ Technology’s effectiveness doesn’t depend on constant human intervention or try to infer intent based on TTPs.
Unlike invasive monitoring approaches, DTEX InTERCEPT anonymizes user intelligence and collects only the minimum amount of metadata necessary to build a forensic audit trail and identify risky behaviors, which never slows network, endpoint or user performance. This allows DTEX’s Insider Risk Management approach to scale the solution quickly to hundreds of thousands of endpoints with continuous visibility in near real-time. DTEX requires less than 0.5% CPU per endpoint and collects only 3-5MB of data per user per day, creating no perceivable network, employee productivity, or endpoint performance impacts.
In our next post discussing critical factors when comparing Insider Risk Management and Insider Threat Surveillance solutions, we will cover behavioral analytics and their role in understanding key differences between these two types of solutions.
Subscribe today to stay informed and get regular updates from DTEX Systems





