DTEX Is Different
We pioneer solutions built around people: the most intelligent enterprise sensor you have. Discover how we’re improving workforce cyber intelligence and security while still prioritizing employee privacy.
Dive deeper into our lightweight cyber security and workforce intelligence platform with an interactive tour that shows how we continuously translate real-time telemetry about human activities, behaviors, and communications for immediate insights into security challenges, employee engagement, and more.
Two Human-Centric Platforms
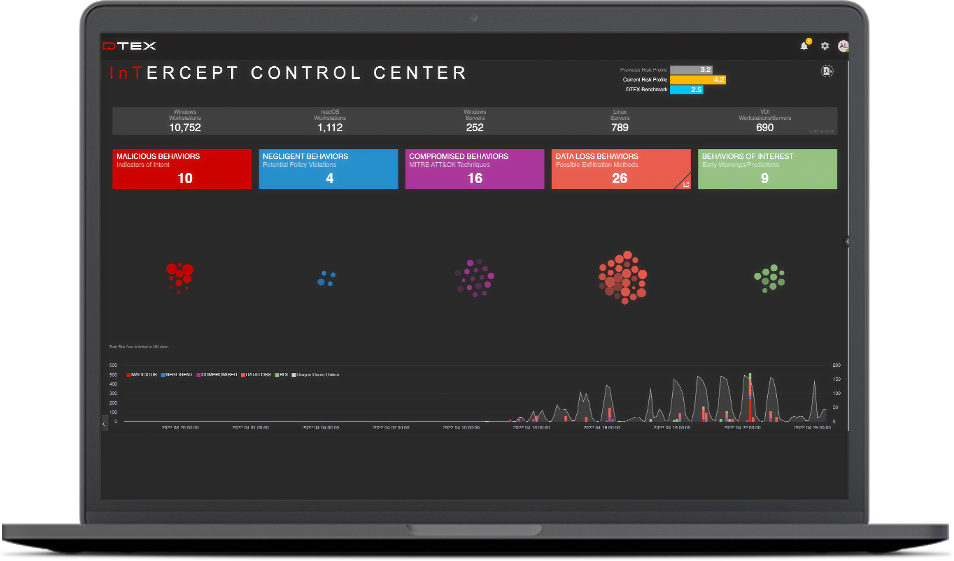
DTEX InTERCEPT
DTEX InTERCEPT consolidates the essential elements of Data Loss Prevention, User Behavior Analytics, and User Activity Monitoring in a single light-weight platform to detect and mitigate insider risks well before data loss occurs. Combining AI/ML with behavioral indicators, DTEX enables proactive insider risk management at scale without sacrificing employee privacy or network performance.
InTERCEPT is a scalable, cloud-native platform. Through its patented and privacy-compliant metadata collection and analytics engine, the DTEX platform surfaces abnormal behavioral “indicators of intent” to mitigate risk of data and IP loss, enabling SOC enrichment with human sensors and empowering enterprises to make smarter business decisions quickly.
2023 Insider Risk Investigations Report
This report identifies a significant increase in corporate IP and data theft incidents, the Human Resources department’s growing role in cybersecurity, and notable new trends impacting the insider risk landscape due to the rise of employee attrition.
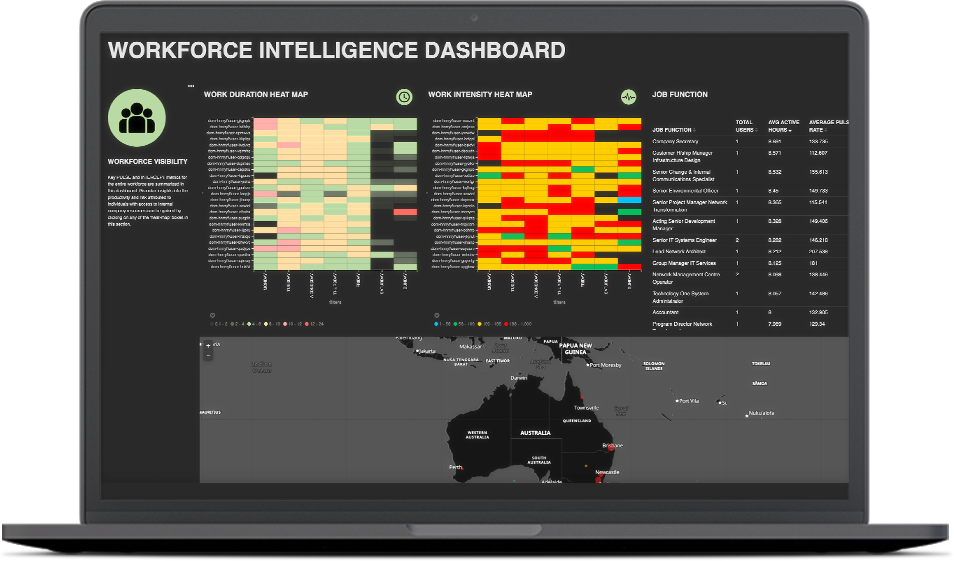
DTEX PULSE
DTEX PULSE enables organizations to learn from their workforce by anonymizing an employee’s physical interactions with organizational assets, aggregating these interactions across the entire business, and then performing analysis to understand engagement levels without compromising privacy.
A Modern Approach to Employee Engagement and Well-being
Workforce Cyber Intelligence supports digital transformation initiatives and human capital management programs by non-intrusively measuring employee engagement and identifying opportunities for cost, performance, and operational efficiencies.
Workforce Cyber Intelligence & Security Use Cases
By collecting and analyzing employee and third-party interactions with data, machines, and applications, Insider Risk Management through behavioral intelligence supports a wide range of use cases:
Supporting Employee Wellness
Help organizations identify employees at risk of burnout.
Optimizing Asset and License Utilization
Reveal why employees are using enterprise assets to help IT and procurement teams understand what’s working and what’s not.
Protection from Insider Threats
Identify patterns of behavior to prevent threats before they become realized risks.
Remote Workforce Security
Protect WFH employees beyond corporate firewalls or network proxies.
Employee Engagement
Inform conversations about individual performance, professional development, and growth strategies.
Informing Financial and Operational Planning
Measure team performance to aid planning.
Data Loss Prevention
Understand malicious intent long before traditional DLP measures are triggered.
GDPR Compliance
Anonymize data to satisfy GDPR requirements.
Reducing Legal Liability
Identify the personal online activities that put the enterprise at risk – while protecting employee privacy.
Monitoring Employees
Enable monitoring without violating trust or privacy.