The Covid-19 pandemic and the rapid, forced adoption of a remote workforce has changed how organizations do business. It has also affected opportunities for insider threats. For the DTEX 2020 Insider Threat Report we spoke with hundreds of businesses across a wide range of industries to learn about those changes. For example, what does it mean when an employee uses Incognito mode, downloads a Tor browser, or bypasses the corporate VPN? All three activities obfuscate the employee’s actions. The job of security is to determine if the person is simply protecting their own privacy, masking behavior that violates company policies, or attempting to hide an attack.
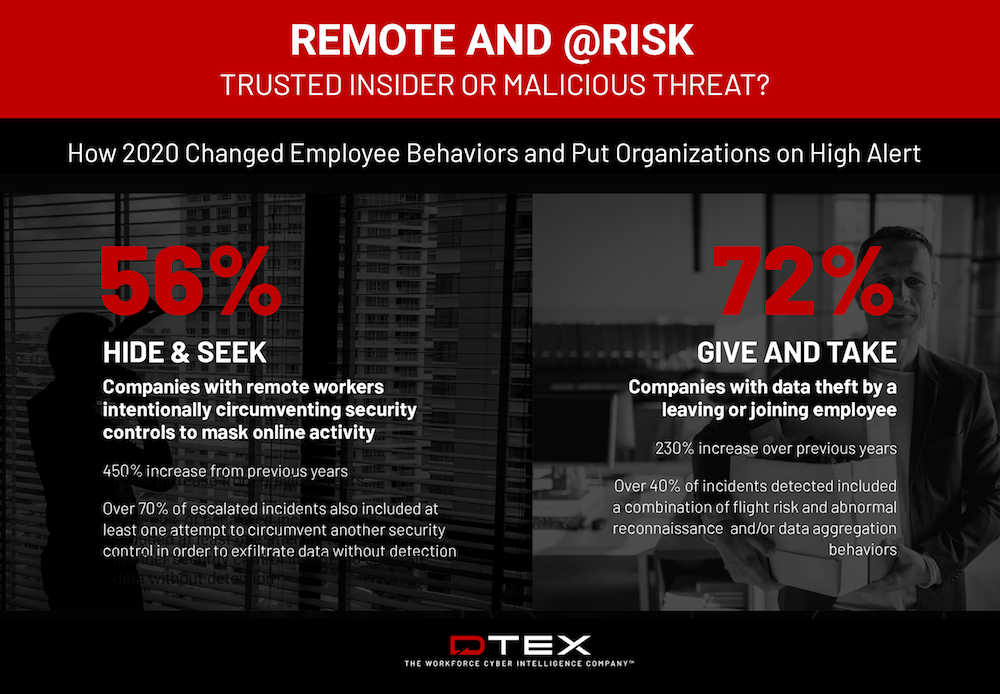
In 2020, we saw a 450% increase in obfuscation activities when compared to 2019. 56% of the companies surveyed reported remote workers intentionally bypassing the corporate VPN to obfuscate activities. Within these incidents, a clear majority of the behaviors – 70% – were malicious, including at least one attempt to circumvent another security control to exfiltrate data without detection.
Organizations always worry about their intellectual property when an employee leaves, in particular when one leaves to join a competitor. When they are in the office and on the corporate network, controlling access to and exfiltration of IP can be difficult. Salespeople need access to customer lists and plans and engineers require access to design documents and source code.
When an employee is leaving, they may perform “reconnaissance” to test defenses and identify sensitive information or aggregate and compress files they wish to extract. How does the Work from Home movement affect the actions of disgruntled employees?
Again, a big increase in suspicious and malicious activity. In 2020, 72% of the organizations reported data theft activities by an employee leaving or joining a company – a 230% increase over 2019.
Protecting sensitive information against malicious insiders is always a balancing act. Organizations want to identify actions that put intellectual property or customer data at risk, but while not invading the privacy of employees. In the next blog post on the report we will discuss how employees mask their online activities and how organizations can discern between benign, unsafe, and malicious employee actions.
The full report is available for download here: https://www2.dtexsystems.com/Insider-Threat-2020-Blog