The rise of foreign interference and high-profile breaches has highlighted the need to address the human element in cybersecurity through a proactive insider risk program.
In many ways, Australia is leading the way in this area of reform. The Security of Critical Infrastructure (SOCI) Act is perhaps the strongest display yet, mandating critical infrastructure operators to establish and comply with a Critical Infrastructure Risk Management Program (CIRMP).
The CIRMP “aims to ensure responsible entities take a holistic and proactive approach toward identifying, preventing, and mitigating risks”. This includes malicious and non-malicious insider risks in an organization and its supply chain.
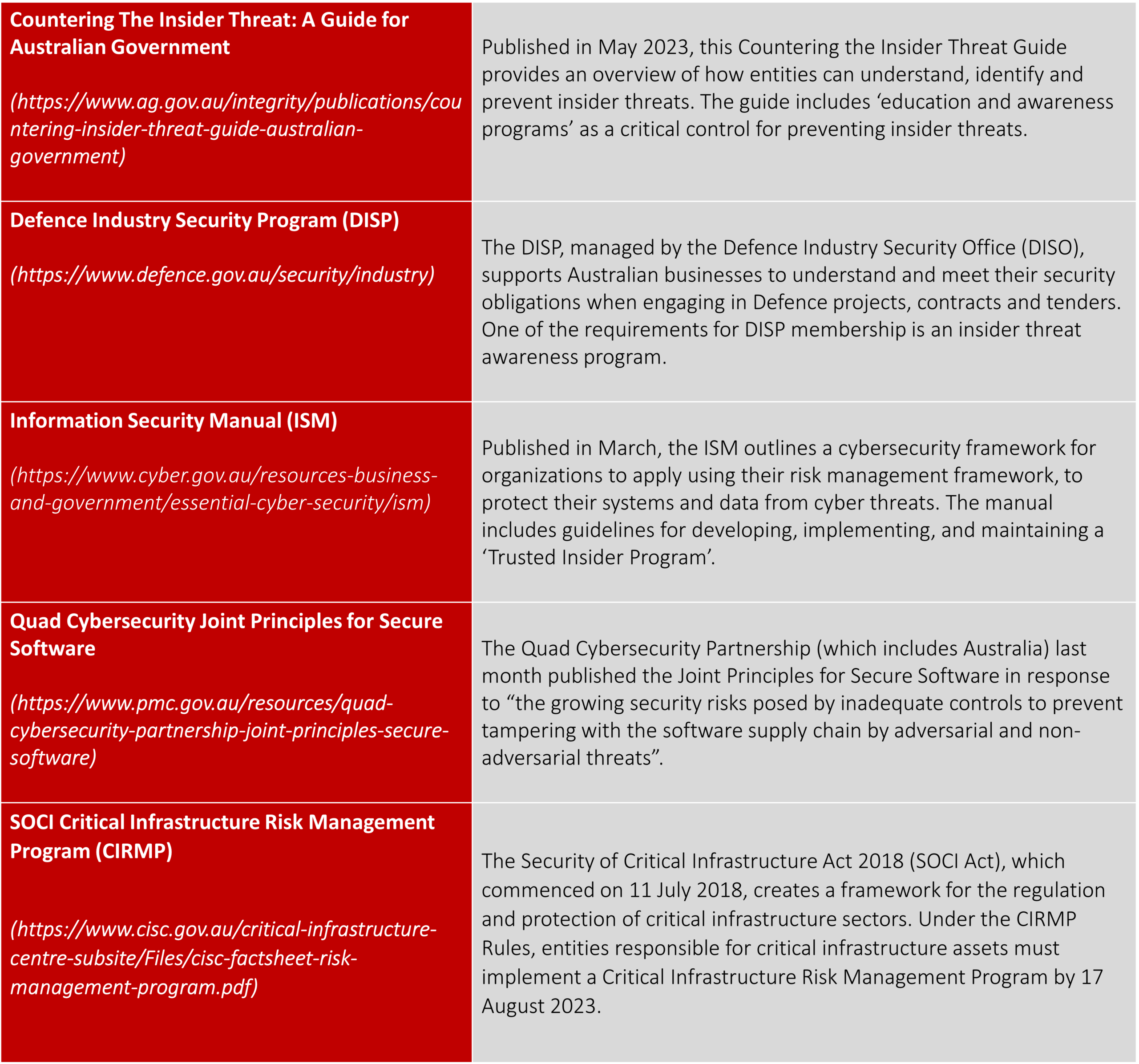
But that’s not all. There have been several frameworks developed for establishing an insider risk program, or a trusted insider program. These include:
Legislation is Coming: Prepare Now with an Insider Risk Program
With human-initiated cyber breaches on the rise, it is encouraging to see such momentum around building an insider risk program. But with so many guidelines from different entities, it can be hard to keep up or to know what is right. There are also several misconceptions on insider risk programs that must be overcome.
A solid insider risk program can afford organizations the chance to prevent insider risks from becoming threats in the first instance. They can prevent data loss and uplift culture to one of a trusted workforce, where security is BAU. It might sound like a pipedream, but with the right governance, data, systems and processes in play, it’s entirely achievable.
Given the evolving threat landscape, it’s only a matter of time before more insider risk program regulations come into law. No doubt failure to comply will come with a set of consequences.
With that in mind, now is the perfect time to home in on your insider risk capability maturity with a holistic and programmatic insider risk program.
The DTEX i3 Team has extensive experience with enabling organizations within government and critical infrastructure to flesh out their insider risk programs. Comprising behavioral researchers, consultants and an elite team of insider threat investigators, our i3 Team is well positioned to help you create an intelligence-driven, investigation–ready capability.
Contact DTEX for support in building or maturing your insider risk program

