Covid-19 is sooo 2020! Data breaches, ransomware, and cybercrime are trending this year, and sadly, it doesn’t seem like they are slowing down.
Over the last few years, everyone has been dealing with Covid-19, and now we are all being attacked by cyber criminals that want to steal our data, and no one is immune. Similar to how medical professionals have handled Covid-19, security teams are trying to reduce the risk and impact of a data breach. And like medical professionals dealing with an evolving situation, those of us in security are trying to keep up with the evolving threat landscape. We are constantly monitoring our systems, isolating the critical ones as much as possible, and staying on top of patching so our security “boosters” are up to date. With Covid-19, most people have accepted this virus is something we will need to live with. We, as a society, may need to accept the fact that we are likely to be affected by a breach at some point and everyone should practice good cyber hygiene to help minimize the risk and impact of a data loss event.
In the last year, the DTEX i3 Team has seen an uptick in cloud-based shadow IT. Most employees are trying to be more efficient with their work and many of them just aren’t well versed in security. Staff across a variety of departments are setting up publicly accessible shared dashboards to analyze data—many of these dashboards contain sensitive information about the company, its contractors, employees, and in some instances, physical security. A threat actor could leverage this information to commit a targeted phishing attack, a business e-mail compromise or worse. We have also seen a significant increase in publicly-accessible portals setup by suppliers; some of these portals do not enforce session logout and are a data breach waiting to happen, assuming it hasn’t happened already, as in the case of Telstra.
Our team is constantly providing our engineers with real world insights that improve the capability of our software and give our clients added value. With the continuous identification of potential new attack vectors being added to our platform, DTEX InTERCEPT offers a holistic view of potential security risks within an organization; we not only detect data loss and insider threats, but we give insight into the security of those cloud-based applications that are part of your supply chain or maybe they are shadow IT. The visibility that InTERCEPT provides will help security teams quickly identify any portals being accessed by staff and will give them the opportunity to verify they are approved and more importantly, secure.
A few examples of insecure portals that we have seen across a range of clients and industries include:
- E-Discovery portals being used by legal teams
- Compliance portals used for mandatory continuing education of medical staff
- E-Learning portals used across many industries
- IT/OT portals used by entities interacting with critical infrastructure equipment
- Employee reward portals
- Cloud-based HR tools used for performance review
- Cloud-based dashboards integrated with software like Power BI and are being used to analyze sensitive data
- Collaboration tools that contain shared dashboards with sensitive information
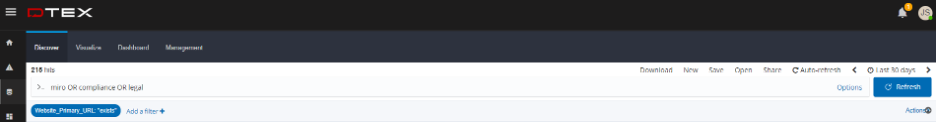
InTERCEPT can be proactively used to identify gaps in security with your supply chain and shadow IT instances by actively looking for the “unknown.” An example of how to identify any insecure shared dashboards or open portals is depicted below. Your analyst team will need to spend some time eliminating the “known,” for example, SharePoint, which may be an approved tool, and then look for the “unknown.” In the image below, the analyst is targeting keywords that may indicate a URL to a cloud-based SAAS potentially setup by an employee. These keyboards can also be replaced with URL components, like “gid=0” to show any Google Sheets that may be unprotected or “usp=sharing” to identify potentially unprotected Google Drive sites. By continuously identifying new technologies, especially collaboration and productivity tools, your analysts can actively hunt for potential attack vectors into the organization.
With InTERCEPT and the DTEX i3 Team working with you to help reduce the risk of data loss, insider threats and supply chain risk, your organization will be in the best shape possible to avoid an event that may take months, or longer, to recover.
Request a demo now to learn more.
