WORKFORCE CYBER
INTELLIGENCE AND SECURITY
BLOG
A Human-centric Approach to Operational Awareness and Risk Management.

THE LATEST ON WORKFORCE CYBER INTELLIGENCE

DTEX i³ Threat Advisory Provides Detections for LOTL, C2 Abuse
Workspace applications are increasingly being weaponized as a Living off the Land (LOTL) technique, as threat actors find new ways…
Read More
Countering Foreign Interference: 2024 Insider Risk Report Takeaways
There has been no shortage of incidents related to foreign interference and IP theft. From theft of…
Read More
DLP for the Virtual Enterprise with DTEX InTERCEPT
Legacy Endpoint Data Loss Prevention (DLP) solutions have left organizations with a mountain of challenges and many headaches. With the…
Read More
Insider Risk Mitigation Strategies – New Gartner Market Guide
On December 29th Gartner analysts Jonathan Care, Brent Predovich, and Paul Furtado published the first ever Market Guide on Insider…
Read More
Insiders Strike Again at Tesla… or did they?
News broke on January 22 that Tesla has filed a federal lawsuit accusing Alex Khatilov of stealing upwards of 26,000…
Read More
The 5 Reasons Why Enterprises Are Upgrading to Modern Endpoint DLP
Companies worldwide have spent billions of dollars on first generation endpoint data loss prevention (DLP) technologies, hoping it would be…
Read More
2021 Remote Workforce Security Report: Organizations Still Lack Confidence in Security Practices
Even with news of successful vaccines in production, most of us know that Covid-19, and the challenges brought along with…
Read More
2020 Insider Threat Report - Conclusion
The 2020 DTEX Insider Threat Report shows that the Work From Home movement has helped reveal a blind spot in…
Read More
The Insider Threat Kill Chain – Obfuscation
In cybersecurity, the kill chain refers to the sequential steps an adversary must complete in a successful attack. Stopping the…
Read More
The Insider Threat Kill Chain - Aggregation
In the previous postings on the Insider Threat Kill Chain we covered how malicious insiders (whether persistent insider threats or…
Read More
2020 Insider Threat Report - Give & Take
We previously discussed the dramatic increase in obfuscation activities found in the DTEX 2020 Insider Threat Behavior Report. More than…
Read More
The Insider Threat Kill Chain - Circumvention
In our previous post on the Insider Threat Kill Chain we discussed how indicators of Reconnaissance efforts are different for…
Read More
2020 Insider Threat Report - Hide & Seek
As noted earlier, the DTEX 2020 Insider Threat Behavior Report surveyed hundreds of customers and Global 5000 organizations to learn…
Read More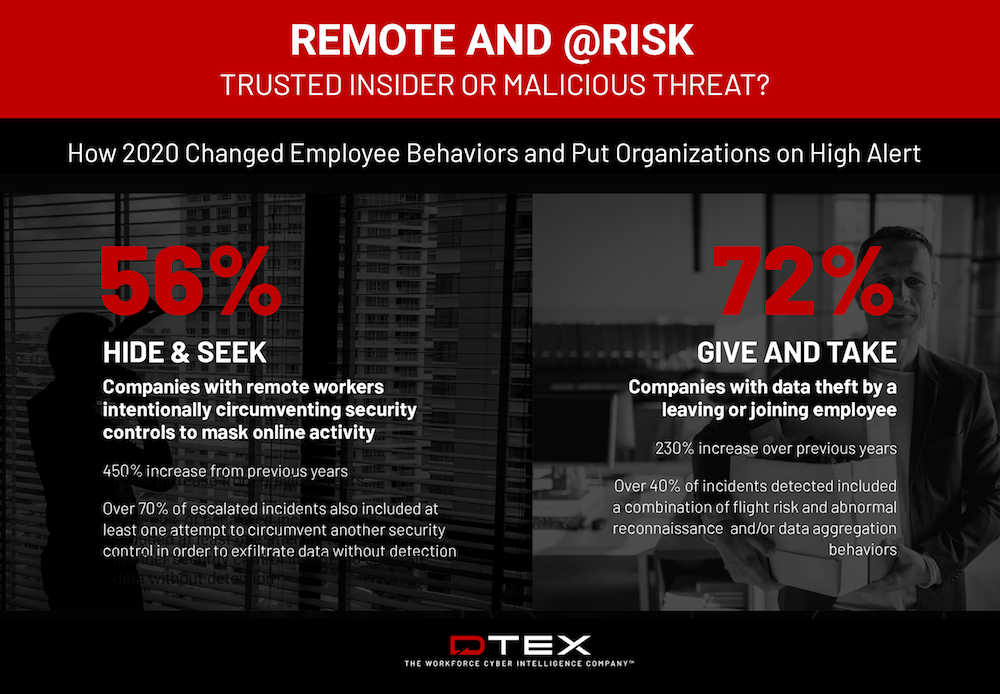
2020 Threat Report: Remote and @Risk - Trusted Insider or Malicious Threat
The Covid-19 pandemic and the rapid, forced adoption of a remote workforce has changed how organizations do business. It has…
Read More