Next-Gen Human Intelligence, Endpoint Telemetry & Digital Forensics
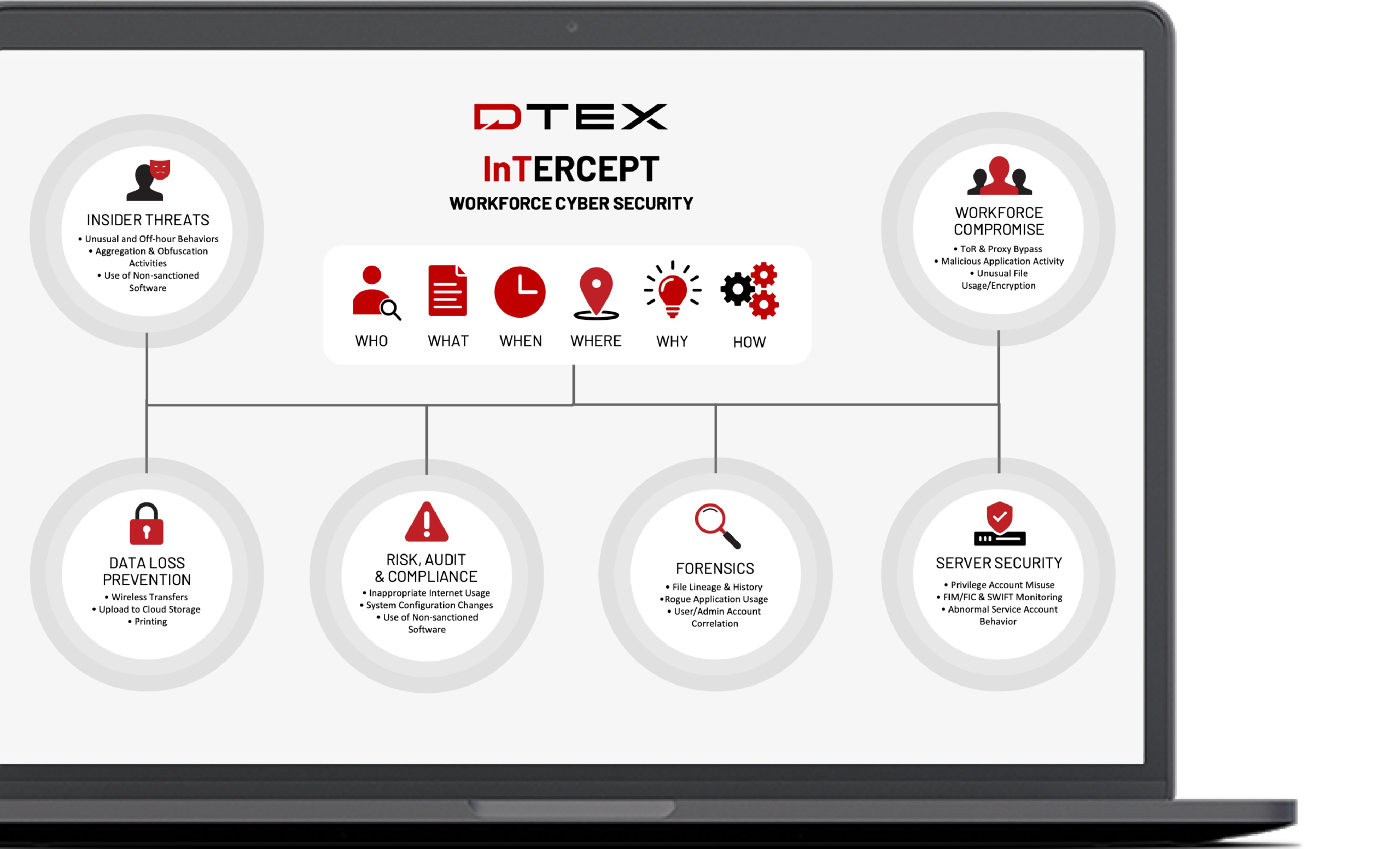
As part of the CrowdStrike Store, customers can seamlessly deploy DTEX InTERCEPT Behavioral DLP capabilities within the CrowdStrike Falcon platform to gain real-time, contextual behavioral intelligence that answers How, When, Why, Where and What sensitive IP and other data files every employee and third party is interacting with, aggregating, archiving, modifying, obfuscating, and may be attempting to exfiltrate.
Customers also gain access to DTEX Systems’ digital forensics intelligence to enable push-button compilation of an evidentiary quality audit trail of user activities to enrich incident response investigations.
Download the DTEX InTERCEPT Solution Brief for CrowdStrike Falcon.

Risk-Adaptive Data Loss Prevention
DTEX InTERCEPT for the CrowdStrike Falcon® platform protects sensitive data and IP from leaving an organization with multiple, highly accurate and dynamic enforcement capabilities. Data loss is prevented intelligently when a user’s behavioral risk score exceeds an organization’s threshold by blocking specific application processes and network connections that are not part of normal or approved workflows.

Insider Risk Mitigation & Workforce Analytics
DTEX InTERCEPT for the CrowdStrike Falcon platform demystifies the context and intent of human behaviors without violating the trust and privacy of employees. Alert stacking and activity scoring algorithms accurately detect deviations that indicate credential compromise, precede ransomware infection and predict malicious insider intent and activity.
The latest Research on Workforce Cyber Intelligence & Security

2022 Insider Threat Report
As the Work-from-Anywhere environment continues to evolve, it has given rise to a new persona: The Super Malicious Insider. One with superior technical skills, in-depth knowledge of common insider threat detection techniques, and the opportunity to cause serious damage to your organization.
Download Now
A SANS Product Overview: Smart Enterprise Visibility with DTEX InTERCEPT
No matter the industry, security teams know that the weakest common denominator in the digital enterprise is the user. Whether it be an intentional act or an innocent faux-pas, protecting your organization against insider threats can be an uphill battle when you’re using legacy solutions.
Download Now
2021 DLP Radar: DTEX Named Fast-Moving Leader
This GigaOm report details their best practices for adopting a multi-faceted approach to DLP that is holistic, intelligent and able to apply context to data usage as part of a broader risk management strategy. In addition, you’ll find evaluations of vendors who are offering modern DLP solutions.
Download Now